Defining Continuous Threat Exposure Management
CTEM shifts cybersecurity from counting vulnerabilities to continuously identifying and mitigating real-time exposures in production
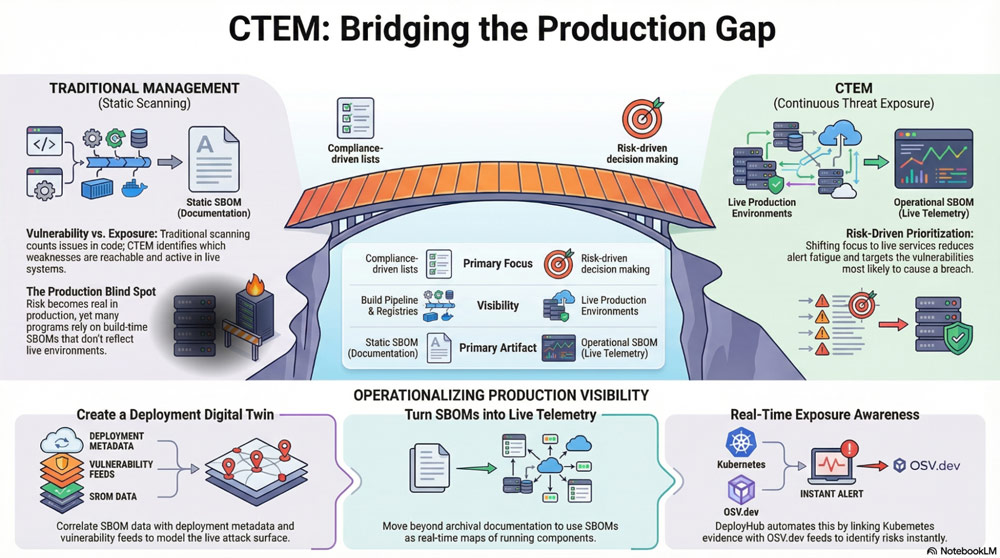
Security teams are starting to hear a new term more often: Continuous Threat Exposure Management (CTEM). This new term, championed by the Gartner analyst, reflects an important shift in how researchers think about vulnerability management. Instead of asking what vulnerabilities exist somewhere in our code, CTEM asks a more practical question: which vulnerabilities actually increase our likelihood of breach right now?
That shift sounds subtle, but it changes everything about how security programs operate.
The challenge is that many CTEM strategies are still missing one critical ingredient, visibility into what’s actually running in production.
If you don’t know what’s deployed, you don’t really know what’s exposed. And exposure, not inventory, is what attackers care about.
What is Continuous Threat Exposure Management (CTEM)?
Continuous Threat Exposure Management (CTEM) is a modern approach to cybersecurity that focuses on a structured lifecycle for identifying and reducing exposures that adversaries could exploit.
CTEM is a way of thinking about security that focuses on what’s actually at risk right now, not just what vulnerabilities exist somewhere in your code or systems. It’s about continuously spotting exposures, understanding which ones matter, and acting before attackers can exploit them.
Continuous Threat Exposure Management isn’t a one-time exercise or a checklist—it’s an ongoing process. It combines real-time visibility into what’s deployed, vulnerability intelligence, and risk prioritization to help security teams focus on the issues that truly matter. Instead of reacting to long lists of potential vulnerabilities, teams can concentrate on live exposures in production, where threats can actually impact the business.
CTEM Is About Exposure, Not Just Vulnerabilities
Traditional vulnerability management often emphasizes counting issues found in SAST scans, container images, SBOMs, or dependency checks. This approach can create long lists of potential vulnerabilities—but many of these may never be exploitable in live environments.
CTEM flips the focus:
- Reachable: Is the vulnerability actually accessible in production?
- Exploitable: Can an attacker use it?
- Relevant: Does it exist in an environment that impacts business risk?
This shift moves organizations from compliance-driven reporting to risk-driven decision-making, prioritizing what truly matters.
The CTEM Cycle: Steps for Continuous Risk Management
CTEM works as a repeating cycle, each step feeding into the next to maintain a real-time understanding of exposure:
1. Discovery
Identify all deployed assets, services, and dependencies across environments. This goes beyond build-time SBOMs and static inventories to include live production systems.
2. Continuous Visibility
Maintain up-to-date knowledge of what is actually running. Modern deployments are ephemeral—containers rebuild, microservices redeploy, and infrastructure scales dynamically. Visibility is key to understanding real exposure.
3. Assessment & Correlation
Correlate deployed assets with SBOM contents, vulnerability intelligence feeds, and environment topology. This creates a deployment digital twin, a living map of what’s running and what’s vulnerable.
4. Risk Prioritization
Focus remediation efforts on exposures that matter most. Ask: “Is this vulnerability exploitable here, now, and in a high-impact context?” This step reduces alert fatigue and wasted effort on irrelevant findings.
5. Remediation & Mitigation
Apply fixes, configuration changes, or compensating controls to reduce exposure. Because the process is continuous, teams can react quickly to newly disclosed vulnerabilities affecting live systems.
6. Monitoring & Feedback
Continuously monitor for new exposures or changes in production. Feed insights back into the cycle to improve detection, assessment, and prioritization over time.
Production Is Where Risk Becomes Real
For years, most security tooling has concentrated on the build pipeline. Static analysis inspects source code, dependency scanners evaluate open-source packages, container scanners examine images before release, and SBOMs capture package composition at build time. These steps are valuable and necessary. But attackers target running systems.
They go after exposed APIs, deployed services, misconfigured infrastructure, privileged identities, and vulnerable components that already live inside environments. A vulnerability that never ships is harmless. A vulnerability running in production is an exposure.
That’s why CTEM only becomes meaningful when it includes post-deployment visibility.
Many CTEM Programs Still Have a Blind Spot
One of the biggest surprises I see when organizations start talking about CTEM is how often they assume their inventories reflect reality. Common assumptions include:
- SBOMs represent what’s actually running in production
- Scanners accurately identify what’s exposed
- Asset inventories are complete and up to date
In modern environments, these assumptions break down quickly.
- Containers rebuild automatically
- Microservices redeploy constantly
- Dependencies change between environments
- Infrastructure scales dynamically
- New vulnerabilities appear after deployment—not before it
Without connecting SBOMs and vulnerability intelligence to real deployment evidence, CTEM risks becoming just another scanning exercise instead of an exposure-management strategy.
Post-Deployment Visibility Changes How Teams Prioritize Risk
When security teams can see what is actually deployed, their priorities shift almost immediately. Instead of reviewing thousands of possible vulnerabilities across repositories and images, they can focus on the subset that exists inside live environments. Instead of guessing whether something is reachable, they can see where it is running and how it connects to other services. Instead of reacting to noise, they can respond to exposure.
This dramatically reduces alert fatigue and improves response time when new CVEs appear. The most important question shifts from is this vulnerable somewhere? to is this vulnerable here?
That’s the question CTEM is designed to answer.
SBOMs Become Operational Instead of Archival
SBOM adoption is accelerating across industries, but many organizations still treat SBOMs as documentation artifacts generated during builds and stored for compliance purposes.
Inside a CTEM strategy, SBOMs become something much more powerful. When they are correlated with deployment metadata, they provide continuous visibility into which vulnerable components are actually running in which environments. Instead of static snapshots, they become live telemetry supporting real-time exposure awareness.
This is how organizations move from simply generating SBOMs to actually understanding their attack surface.
CTEM Needs a Deployment Digital Twin
To work well, CTEM requires a continuously updated model of what’s deployed across environments. Many teams are starting to think about this as a deployment digital twin, a living representation of applications, services, dependencies, and endpoints as they exist in production.
A deployment digital twin connects SBOM contents to deployment metadata, environment topology, and vulnerability intelligence feeds. That connection makes it possible to immediately identify when newly disclosed vulnerabilities affect running systems instead of waiting for the next scan cycle or manual investigation.
Instead of repeatedly scanning endpoints and hoping results reflect reality, teams gain continuous exposure awareness.
That’s what makes CTEM actionable.
Where DeployHub Fits into a CTEM Strategy
This is exactly the gap DeployHub is designed to close.
DeployHub builds a deployment digital twin by correlating SBOM data with pipeline metadata, registry artifacts, Kubernetes deployment evidence, and vulnerability intelligence feeds like OSV.dev. The result is a clear picture of what is actually running across environments and which vulnerabilities affect those systems in real time.
Instead of chasing long scanner reports, teams can focus on vulnerabilities that impact live services and prioritize remediation based on actual exposure. That shift reduces unnecessary work while improving response time to newly disclosed risks—two outcomes that are central to making CTEM effective.
CTEM Starts with Discovery but Succeeds in Production
CTEM represents a meaningful evolution in how security teams manage risk. It encourages organizations to think continuously about exposure rather than periodically about vulnerabilities.
But exposure doesn’t live in source code repositories or container registries. It lives in running systems.
Organizations that extend CTEM into post-deployment environments gain faster response to new vulnerabilities, clearer attack-surface awareness, and a much stronger ability to prioritize what actually matters.
CTEM may begin with discovery, but it succeeds in production.