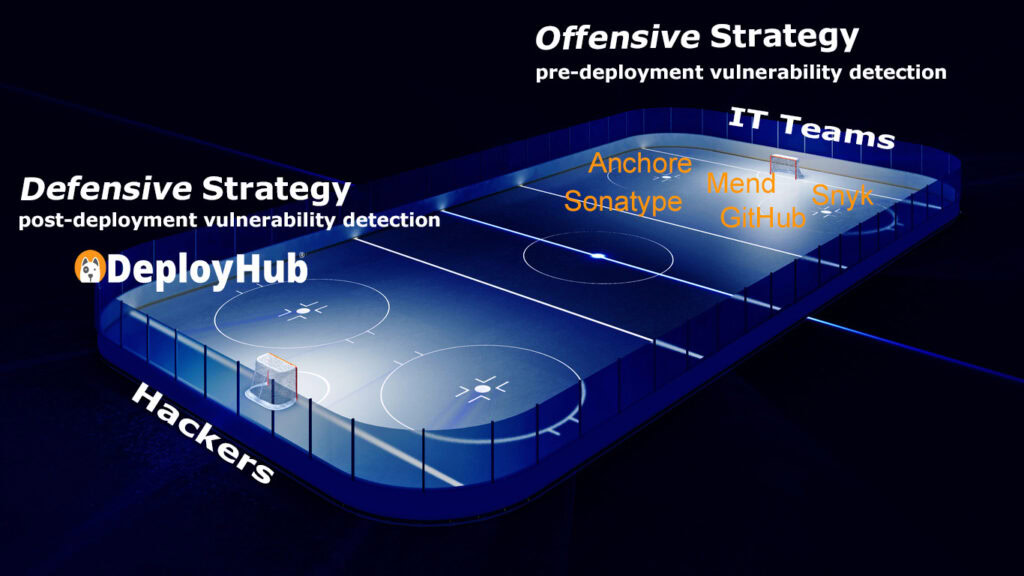
When it comes to software security, most organizations play offense, but few have a solid defense.
In DevSecOps, offensive tools dominate the early game. These include static application security testing (SAST), software composition analysis (SCA), and CI/CD scanners that detect vulnerabilities before code is deployed. Think of them as the offense: their job is to find weaknesses in your own codebase and dependencies while your team “has the puck.”
Tools like Snyk, SonarQube, and GitHub Advanced Security excel at this phase. They identify problems before release, ensuring your team doesn’t ship known vulnerabilities into production. It’s an important part of the play — but the game doesn’t end when you push to production.
Protecting software through the complete lifecycle requires a post-deployment security defense strategy grounded in vulnerability remediation best practices, not just more scanning.
You Can’t Win with Offense Alone. Post Deployment Security Needs Defense.
The Game Changes After Deployment
Once software is deployed, the puck changes sides. Suddenly, you’re no longer in control; attackers are. Vulnerabilities continue to emerge in the open-source components you depend on. A library that was safe yesterday could have a critical CVE today.
Offensive tools stop watching once code leaves the pipeline. That’s when your post-deployment vulnerability defensive strategy needs to take over, monitoring what’s live, seeing which CVEs are truly exploitable, and automatically coordinating response across the deployed environments.
Playing Defense After Deployment
What is missing is a platform for this second half of the game, when the opposing team has the puck. A post-deployment vulnerability defense strategy is required to continuously detect and accelerate remediation in deployed systems without intrusive agents or manual rescanning.
Why Post-deployment Vulnerability Defense Matters
A pure offensive posture leaves a blind spot in open-source vulnerability management. Once your software is live, your CI/CD tools go silent. Attackers, however, don’t stop probing. Without visibility into live vulnerabilities, organizations delay response, increasing risk and time-to-remediation. According to industry experts, it takes 90-120 days to remediate a single ‘live’ vulnerability.
It gives IT teams a real-time defensive view, connecting SBOM data, component versions, and deployment intelligence, to know exactly which applications are exposed and how to defend them.
From Offense to Defense: A Complete Security Game Plan
Winning teams need both offense and defense:
- Offense: SCA, SAST, and code scanning during build time (preventive)
- Defense: A DevSecOps defense strategy that includes Post-deployment detection and remediation (responsive).
Playing Defense After Deployment
Post-deployment vulnerability defense closes this gap. It focuses on continuously tracking new open-source security vulnerabilities that impact live systems, building a strong software supply chain defense. It supports edge, cloud-native, HPC, space vehicles and the ground systems they rely on.
Post-deployment security monitoring protects live environments using SBOM intelligence. When a new open-source CVE hits, post-deployment monitoring shows you:
- Which applications are affected
- Where they’re running
- Who owns the fix
That’s not just detection — it’s defense.

DeployHub’s Defensive Strategy
DeployHub provides post-deployment vulnerability detection, a defensive approach that focuses on what’s real and running. Instead of rescanning source code, DeployHub builds a digital twin of your deployed software. By maintaining a “digital twin” of your deployed software, DeployHub maps every open-source component version across applications, components, and environments. When a new CVE emerges, DeployHub instantly shows where it lives in production, across your entire software estate, supporting developers in a coordinated defense response to patch or mitigate the threat before it’s exploited.
DeployHub continuously synchronizes with OSV.dev every 10 minutes, pulling the latest open-source vulnerability data from trusted sources. By correlating this data against your SBOMs, which are mapped to active endpoints and application versions, DeployHub identifies vulnerabilities across live systems in near real time. This ensures that as soon as a new CVE is published, you know exactly which deployed assets are impacted, without intrusive endpoint agents or manual rescanning.
By tracking open-source and third-party packages across environments, DeployHub cuts through the noise. It prioritizes vulnerabilities based on live deployment data, helping teams focus on the threats that truly matter. Developers fix faster, security teams report with confidence, and platform engineers maintain uptime without interruption.
By integrating DeployHub into your software delivery workflow, you extend your security posture from build-time awareness to live defense, ensuring continuous protection even after release.
DeployHub doesn’t replace your offensive tools; it completes them. Together, they form a full-cycle strategy: Offense prevents vulnerabilities from being released. Defense ensures they don’t become exploited in the wild.
The DeployHub Platform
- DeployHub turns SBOM vulnerability management into a continuous defensive process
- Gives developers real-time awareness and automated insights
- Enables continuous monitoring, quickly assessing vulnerabilities for fast remediation
- Proactively defending your deployed software
Frequently Asked Questions
How does post-deployment vulnerability monitoring complement pre-deployment security tools?
Pre-deployment tools catch issues before release, while post-deployment monitoring continuously observes live systems, ensuring new vulnerabilities that appear after deployment are detected and addressed.
Can post-deployment monitoring reduce the time it takes to fix live vulnerabilities?
Yes. By mapping vulnerabilities to running components, environments, and responsible teams, organizations can prioritize remediation and act quickly, shortening mean time to remediation (MTTR).
How can ephemeral environments like containers or serverless functions be monitored for vulnerabilities?
Advanced post-deployment monitoring tracks deployed components across dynamic or short-lived workloads, ensuring even transient systems are observed for new threats.
How does post-deployment security monitoring support compliance and audit requirements?
Monitoring platforms can maintain detailed records of vulnerabilities, affected assets, and remediation actions, providing traceable evidence for standards like NIST, FedRAMP, or ISO frameworks.
How do these systems differentiate between exploitable and non-exploitable vulnerabilities?
By correlating vulnerabilities with live deployment context, usage, and configuration data, monitoring platforms can filter out low-risk issues and highlight actionable threats.
Can post-deployment monitoring integrate with existing DevSecOps pipelines and automation tools?
Yes. Effective monitoring platforms can connect with CI/CD pipelines, orchestration tools, and observability stacks to automate detection, prioritization, and remediation.
How frequently should vulnerability intelligence be updated for effective post-deployment defense?
To maintain real-time awareness, platforms should synchronize regularly with trusted vulnerability sources, ideally multiple times per day, to catch emerging threats quickly.
Are agentless monitoring solutions safe for production environments?
Yes. Agentless solutions observe live systems without installing software on endpoints, avoiding performance overhead and minimizing operational risk.
How can multiple environments across cloud, edge, and on-premises systems be monitored consistently?
By mapping deployed components and their versions across all environments, organizations can gain a unified view of vulnerabilities and ownership regardless of infrastructure type.
How can organizations prioritize vulnerability remediation based on business impact?
By correlating vulnerabilities to active applications, services, and operational criticality, teams can focus on fixing the issues that pose the greatest risk to the business first.